Key takeaways
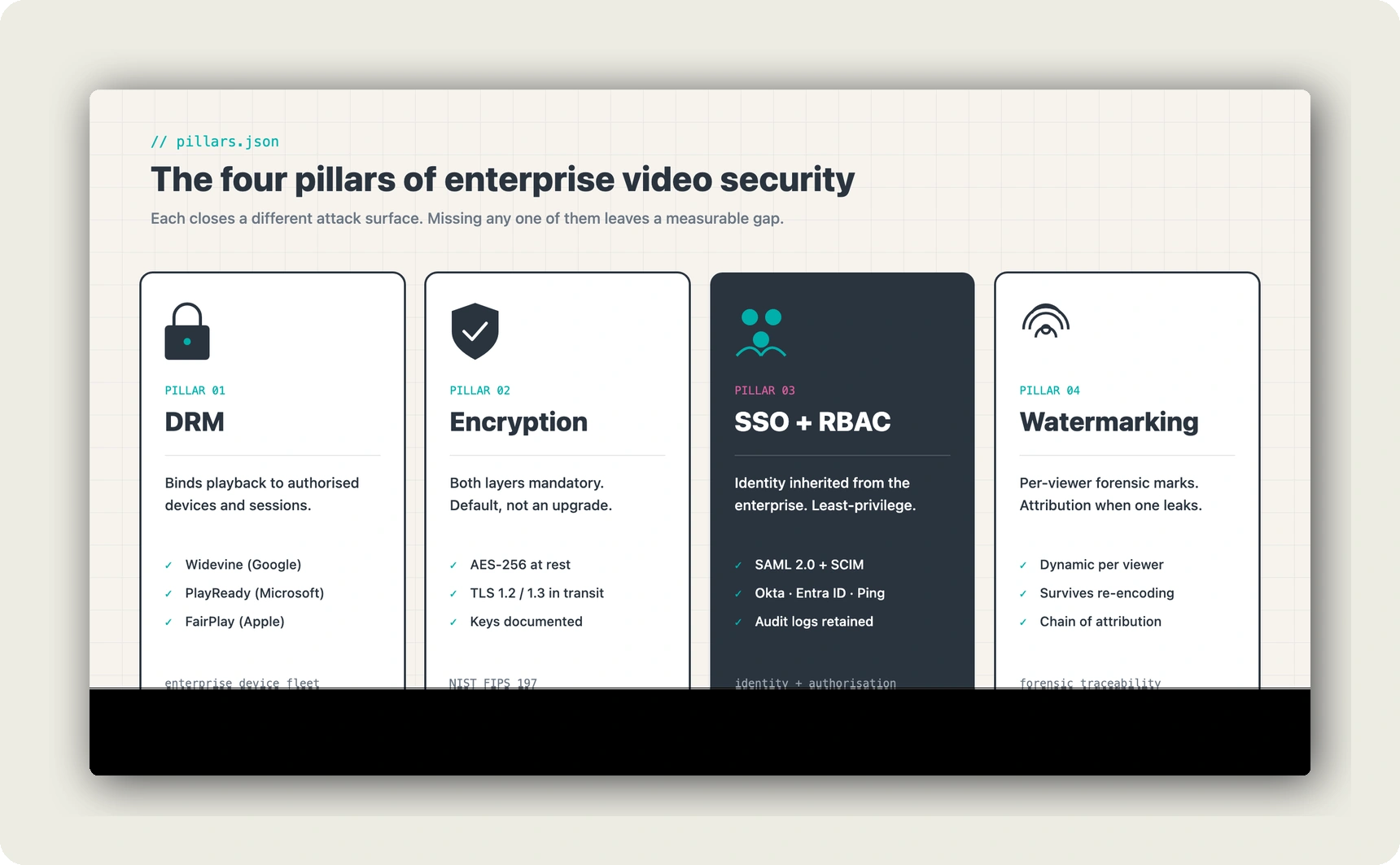
- Enterprise video security is four layered controls, not one feature. DRM, encryption in transit and at rest, authentication plus role-based authorization, and forensic watermarking each close a different attack surface. Missing any one of them leaves a measurable gap.
- GDPR Art. 32 makes the controls mandatory, not optional. The article on security of processing requires appropriate technical and organisational measures proportionate to the risk. For video that carries employee data, customer footage, or protected IP, that is not a light bar.
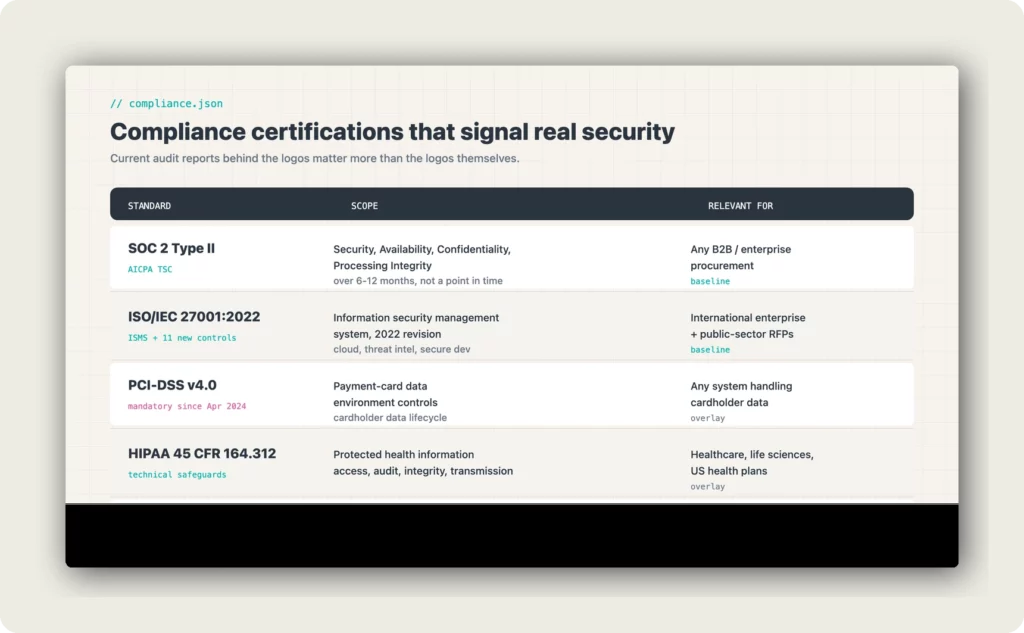
- Certifications signal real security only when the audit report is available. SOC 2 Type II (AICPA TSC) and ISO/IEC 27001:2022 are the baseline. Industry-specific overlays (PCI-DSS v4.0, HIPAA 45 CFR 164.312) apply where data type triggers them.
- The US CLOUD Act (18 U.S.C. §2713) breaks the EU-region promise. US-headquartered providers can be compelled to disclose EU-hosted data to US authorities regardless of which region the console says. For regulated-industry buyers, the legal-jurisdiction line on the vendor contract is the security line.
- A platform-native approach reduces the attack surface versus a stitched stack. When DRM, encryption, SSO, RBAC, and audit logs are one product, one DPA, and one procurement review, exceptions and silent gaps shrink. alugha is built on that model. Current plans on alugha.com/plans.
Why enterprise video security is a board-level question, not an IT checklist
Corporate video carries the content most enterprises would least like to see leaked. Unreleased product footage, internal strategy recordings, executive town halls, paid training, customer-facing support videos containing PII, and partner-only onboarding walk-throughs all live on a video platform somewhere. The security question is not whether the platform claims to protect them. It is which specific mechanisms are in place and which attack surfaces those mechanisms cover.
The regulatory floor is concrete. GDPR Art. 32 requires technical and organisational measures appropriate to the risk of the processing, including encryption of personal data, ongoing confidentiality and integrity guarantees, and the ability to restore availability after incidents. GDPR Art. 83 sets the fine ceiling at €20 million or 4% of global annual turnover, whichever is higher. HIPAA 45 CFR 164.312 names the technical safeguards required for protected health information. PCI-DSS v4.0, mandatory since April 2024, specifies the controls that apply to any system in the payment-card data environment, including video recordings used for fraud review or dispute handling.
When any of these apply, insufficient platform security does not just create risk. It creates documented regulatory exposure that a board, a DPO, or an audit committee will be asked to answer for.
The four pillars of enterprise video security
Enterprise video security works as a layered model. Each of the four pillars closes a different attack surface. A platform that ships three out of four leaves a gap a sophisticated attacker will find, and a regulator will document.
Digital Rights Management (DRM)
DRM binds the playback key to an authorised device and session, so that an intercepted stream or a downloaded file cannot be replayed outside the sanctioned environment. Three systems cover the enterprise device fleet in 2026: Widevine (Google, covers Chrome, Android, Chromecast, most smart TVs), PlayReady (Microsoft, covers Edge, Windows, Xbox, many OTT devices), and FairPlay (Apple, covers Safari, iOS, tvOS). A platform that supports all three avoids the failure mode where a subset of authorised viewers cannot play protected content on the device they actually use.
DRM is not a download-prevention feature alone. It is a policy-enforcement layer: time-bound access, domain restriction, concurrent-stream limits, and offline-playback rules all sit here. For paid training, partner content, or unreleased product footage, DRM is the control that makes the rest of the platform safe to use.
Encryption in transit and at rest
Two layers, both mandatory. Encryption in transit uses TLS 1.2 or TLS 1.3 between the viewer and the delivery edge, and between the content-management system and storage. Encryption at rest uses AES-256 (NIST FIPS 197) on the stored video files and their derivatives (transcoded renditions, thumbnails, subtitle sidecars). The quality signal is that both are default, not an upgrade tier, and that the key-management approach is documented and audited.
The phrase “end-to-end encryption” is used loosely in vendor marketing. For enterprise video it should mean two specific things: encrypted upload and encrypted delivery, with at-rest encryption covering everything between. An HTTPS-only assertion, without the at-rest leg, is a partial answer that does not pass a GDPR Art. 32 review.
Authentication and authorization (SSO, SAML, RBAC)
Authentication answers “is this the person they claim to be”. Authorization answers “is this person allowed to see this video”. Both layers matter, and both need to integrate with the identity systems the enterprise already runs.
- SSO and SAML 2.0 integration. Connectors to Okta, Microsoft Entra ID (formerly Azure AD), Ping Identity, OneLogin, and Keycloak let the video platform inherit the enterprise identity, lifecycle, and MFA policies. Employees log in with existing credentials, administrators offboard in one place, and no platform-specific password sets get scattered across the stack.
- Role-Based Access Control (RBAC). Distinct roles for viewer, editor, publisher, administrator, and auditor. Video-level and folder-level permissions so that confidential product footage stays inside the team that owns it and training content is visible only to the departments that need it. Least-privilege is the default, exceptions are logged.
- Audit logs. Every playback, every permission change, every upload and delete event stamped with user, time, IP, and device context. Logs retained long enough to support incident investigation and regulatory requests.
Watermarking and forensic traceability
Dynamic forensic watermarks embed a per-viewer identifier into the delivered stream. The mark is imperceptible to the viewer, survives re-encoding and screen capture to a measurable degree, and becomes the attribution chain when a leak does occur. For unreleased product videos, pre-launch investor content, or confidential M&A material, watermarking is the control that turns a leak from a forensic dead-end into a traceable event.
In short: DRM locks the door, encryption protects the room, SSO and RBAC decide who gets a key, and watermarking tells you which key was used when a copy still escapes. The four pillars are a set, not a menu.
Compliance certifications that signal real security
Certification logos are common. Current audit reports behind them are less common. For enterprise procurement, a certification matters when it is (a) current, (b) scoped to the services the buyer actually uses, and (c) backed by an available report that the DPO can review.
- SOC 2 Type II (AICPA Trust Services Criteria). Type II, not Type I. The distinction matters: Type I describes design at a point in time, Type II describes operating effectiveness over 6 to 12 months. Cover the Security, Availability, Confidentiality, and Processing Integrity criteria at minimum; Privacy where personal data is involved.
- ISO/IEC 27001:2022. The 2022 revision replaces the 2013 standard and includes 11 new controls reflecting cloud, threat intelligence, and secure development practices. A certificate dated 2022 or later signals alignment with current requirements.
- Industry overlays. PCI-DSS v4.0 for payment data (mandatory since April 2024), HIPAA 45 CFR 164.312 for protected health information, FedRAMP for US federal agency workloads, TISAX for automotive supplier ecosystems, C5 for German public sector. Match the overlay to the data the buyer actually processes.
- GDPR Art. 32 documentation. Not a certification, a regulatory obligation. The platform should provide a documented description of the technical and organisational measures in place, the sub-processor list, the DPA terms, and a clear position on international transfers after Schrems II (CJEU C-311/18).
What the US CLOUD Act does to EU-hosted video
US cloud providers set the performance benchmarks for video infrastructure and offer mature feature sets. That is the honest starting point. The legal question is separate from the technical one. The US CLOUD Act (18 U.S.C. §2713, passed 2018) permits US authorities to compel US-headquartered service providers to produce data under their control regardless of where that data is stored. An EU data-centre selection in the vendor console does not override that statute.
For a regulated-industry buyer, a public-sector procurement, or a German enterprise with a strict DPO, that statute turns the “where is the data” question into “which legal entity operates the platform”. An EU-headquartered provider running on EU/EEA infrastructure removes the CLOUD-Act exposure. The Schrems II ruling (CJEU C-311/18, July 2020) reinforced the same principle for transfers: the legal jurisdiction of the processor, not the region label on the console, determines the protection available.
Six questions to ask every shortlisted video hosting vendor
- Which DRM systems are supported natively, and which require an add-on tier? If Widevine, PlayReady, and FairPlay are not all default, there is a device segment the platform cannot protect.
- Is every upload encrypted at rest by default? Ask for the cipher (AES-256 is table stakes) and the key-management approach. “HTTPS” alone answers only the transit half.
- What is the SSO/SAML integration surface? Which IdPs are supported, is SCIM provisioning available, and how does de-provisioning propagate to active sessions.
- Show the current SOC 2 Type II and ISO/IEC 27001:2022 reports under NDA. Not the logos, the reports. Scope, date, and any noted deviations.
- Which legal entity operates the platform, and is that entity subject to the US CLOUD Act? The answer determines the compliance position on EU-originated data.
- What does an audit log export look like, and how long are events retained? A platform that cannot produce a per-user playback history on request cannot support an incident investigation or a regulator request.
FAQ
What is enterprise video security?
Enterprise video security is the layered set of controls that protect corporate video content from unauthorised access, copying, and redistribution. It combines four pillars: Digital Rights Management (DRM) to restrict playback to authorised devices and sessions, encryption in transit and at rest (TLS 1.2/1.3 plus AES-256) to protect the files themselves, authentication and authorization (SSO/SAML plus RBAC) to control who gets access, and forensic watermarking to attribute leaks when they occur. A complete implementation covers all four pillars alongside relevant compliance certifications (SOC 2 Type II, ISO/IEC 27001:2022) and documented GDPR Art. 32 measures.
Which DRM systems are industry standard in 2026?
Three: Widevine (Google, covers Chrome, Android, Chromecast, most smart TVs), PlayReady (Microsoft, covers Edge, Windows, Xbox, many OTT devices), and FairPlay Streaming (Apple, covers Safari, iOS, tvOS). An enterprise-grade video platform supports all three natively. If DRM is available only on Widevine, the authorised viewers on Apple and Microsoft devices cannot play protected content on the device they actually use.
Does the US CLOUD Act affect EU-hosted video platforms?
Yes, when the platform operator is US-headquartered. Under 18 U.S.C. §2713, US authorities can compel US-based service providers to produce customer data regardless of which country the data is physically stored in. An EU region selection in the vendor console does not override the statute. To remove the exposure, the platform operator itself must be EU-headquartered and outside the CLOUD Act’s scope. Schrems II (CJEU C-311/18) reinforced the same jurisdictional principle for cross-border transfers.
Is alugha certified for enterprise video security?
alugha is built on the EU-hosted architecture described above, with native encryption in transit and at rest, SSO/SAML integration, RBAC, and audit logging. The platform is GDPR-compliant by design, operates under EU jurisdiction (removing US CLOUD Act exposure), and supports the DPA terms enterprise procurement typically requires. Current certification status, scope, and available audit reports can be confirmed with the sales team for specific procurement conversations. Plan details and pricing on alugha.com/plans.
This is a satellite article. For the full pillar, see The Complete Guide to Enterprise Video Hosting.



