Why video hosting in finance, healthcare, and pharma belongs on the desk of the CIO — not just in marketing
Video is a powerful business medium. That is not the problem.
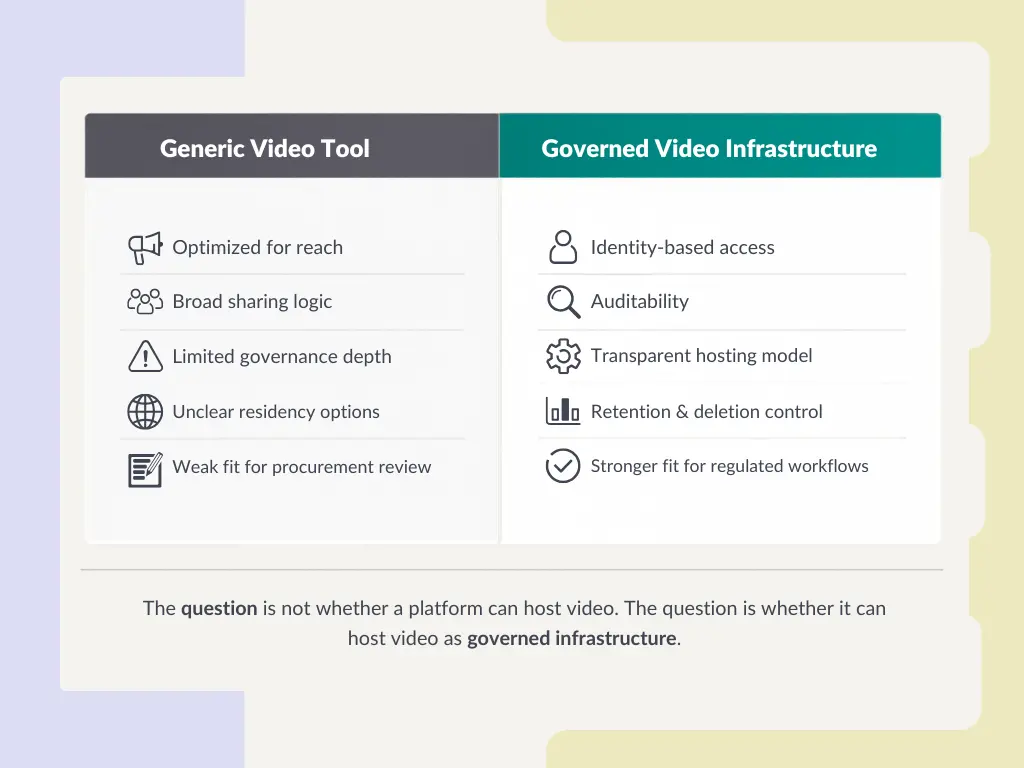
It is also true that many mainstream video platforms are excellent at what they were built to do: distribution, reach, discoverability, convenience. They are fast to deploy. They are familiar to users. And for public marketing content, they can be entirely appropriate.
But as infrastructure for regulated organizations, that is a different question.
I say that without anti-platform rhetoric. The issue is not that public video platforms are “bad.” The issue is that they were built for a different purpose. Who uses them as if they were governed enterprise infrastructure often gives up more control than expected — over access, over data residency, over auditability, and sometimes over the conditions under which critical content is delivered.
That matters in finance. It matters in healthcare. And it matters in pharma and life sciences, where training, quality communication, and internal process alignment are often compliance-relevant by design.
I want to make three points. I want to explain what regulated buyers often overlook when they evaluate video hosting. I want to show the three structural risks that generic platforms create in regulated environments. And I want to end with three questions every CIO, CISO, and compliance lead should now ask internally.
What video hosting in regulated industries really means
Most companies do not buy video infrastructure. They buy a video tool.
That sounds similar. It is not.
A video tool is usually evaluated on playback quality, storage, analytics, branding, and ease of use. Those factors matter. But for regulated organizations, they are only the visible layer.
What matters underneath is whether the platform can operate inside a controlled environment.
Who can access sensitive content? How are permissions managed? What is logged? Where is the data stored? Which subprocessors are involved? Can content be retained for policy reasons and deleted for legal reasons? Can the vendor answer procurement, legal, and security questions clearly — without improvisation?
That is the real threshold.
The common belief is this: if a platform is enterprise-looking, password-protected, and widely used, it is probably suitable for sensitive corporate video workflows.
That sounds plausible. It is not a sufficient test.
A regulated organization does not just need video delivery. It needs governed video delivery.
What is governed video delivery?
Governed video delivery means that the platform is not treated as a media player with storage attached, but as part of the company’s control environment. Access, logging, hosting location, retention, and vendor accountability are not secondary features. They are core requirements.
That is why “video hosting” is often the wrong frame. In regulated industries, the more accurate term is video infrastructure.
And infrastructure decisions belong in IT governance.
Violations of these regulations can result in substantial financial penalties, regulatory enforcement actions, and reputational damage.
Violations of these regulations can result in substantial financial penalties, regulatory enforcement actions, and reputational damage.
What most buyers underestimate
The biggest risk is usually not the video file itself.
It is the workflow around it.
A training video may seem harmless. But if it is shared through weak permissions, hosted in an unclear jurisdiction, or distributed through a platform that offers little audit depth, it can become difficult to defend in an internal review. The same applies to executive communications, internal policy updates, patient education workflows, multilingual training assets, and quality-related SOP communication.
The most important question is therefore not: “Can this platform host our videos?”
The more important question is: “Can this platform host them in a way that we can still explain, govern, and defend six months later — in procurement, in an audit, or after an incident?”
That is where generic platforms often begin to struggle.
They are usually optimized for convenience first. Regulated organizations need convenience, too. But not at the expense of control.
What is data residency?
Data residency describes the legal and physical region in which data is stored and processed. For many European companies, especially in regulated sectors, this is not a technical footnote. It affects procurement, legal review, privacy assessment, and customer trust.
That is not a theoretical distinction. It changes vendor shortlists.
Shortly put: a platform can be easy to adopt and still be the wrong infrastructure decision.
The three risks companies underestimate
1. The access model is often too broad
The first risk is not visible in the demo.
Generic video platforms are often good at sharing. That is precisely the issue. In regulated environments, broad sharing logic can work against the company’s governance model. What looks like usability may, in practice, mean loose distribution, inconsistent permissions, and weak separation between who should see content and who merely can.
Who handles regulated content usually needs more than a link and a password. The platform should fit identity-based access control — ideally through SSO, SAML, MFA, role-based permissions, structured admin rights, and clear user lifecycle management.
That is not feature inflation. It is governance.
The consequence is straightforward: if a company cannot define precisely who may access which content, and under which identity conditions, the platform is not a neutral utility. It becomes a source of exposure.
2. Auditability is often thinner than companies assume
The second risk appears later – usually when someone asks for evidence.
Many vendors claim they offer logs. But the critical question is not whether logs exist. It is whether they are useful.
Can the company reconstruct who accessed a video, when access happened, whether permissions changed, whether a file was replaced, and which administrator made the change? Or does the platform only expose broad usage statistics with limited forensic value?
That difference matters in healthcare training, financial compliance workflows, and life-sciences environments where controlled communication is part of a documented process.
The common belief is this: basic activity data is enough as long as the content is internal.
That sounds practical. It is often wrong.
Internal content is precisely where auditability matters most. Public video is meant to spread. Internal regulated content is meant to remain controlled. Without meaningful logging, companies lose one of the few ways to prove that control existed in the first place.
What is auditability?
Auditability means that a company can reconstruct relevant actions after the fact. In practice, this includes access records, permission changes, administrative actions, and content lifecycle events. In regulated environments, that is often more important than dashboard analytics.
Shortly put: who cannot demonstrate control should not assume control exists.
3. The hosting model may not fit the compliance model
The third risk is often discovered during procurement, not during usage.
A platform can look polished and still create immediate friction the moment security, legal, or compliance asks basic questions: Where is the data stored? Is EU or EEA residency available? Which subprocessors are involved? Can the provider explain how data moves across regions? Can retention and deletion be managed in a way that aligns with company policy?
This is where many generic platforms reveal their real design center. They were not built primarily around governance-sensitive enterprise deployment. They were built around scale, convenience, and broad distribution.
Again, that is not a criticism of their original purpose. It is a mismatch diagnosis.
For regulated organizations, the consequence is structural: the more complex the internal governance environment, the less helpful vague answers become. Procurement slows. Legal review widens. Security pushes back. Business teams become impatient. And a tool that looked simple at the beginning becomes expensive in organizational friction.
That is why data residency, deletion control, and infrastructure transparency should not be late-stage questions. They are first-stage questions.
A concrete scenario
Take a mid-sized pharmaceutical manufacturer with teams in Germany, France, and the United States.
The company wants to roll out multilingual SOP training, quality updates, and internal onboarding videos across sites. The communications team wants speed. HR wants usability. Quality wants traceability. IT wants identity integration. Legal wants clarity on hosting. Procurement wants documentation. Everyone is right.
Now imagine the company selects a generic video platform because rollout is easy and users already know it. Six months later, quality asks who had access to an outdated training asset before it was replaced. Legal asks where related data was stored. Security asks whether external forwarding was technically restricted or merely discouraged. Procurement asks for documentation that was never requested at the start.
At that point, the issue is no longer video.
The issue is governance debt.
That debt is avoidable. But only if the platform is evaluated as infrastructure from the beginning.
The three questions every CIO should now ask
I do not want to argue that companies should stop using public video platforms altogether. That would be simplistic.
For public reach, employer branding, campaigns, and broad distribution, they can remain entirely useful.
The question is not whether such platforms may be used. The question is for what.
Who uses a public-first platform as regulated internal infrastructure should now ask three questions.
1. Where do our sensitive video assets actually live?
Not approximately. Not “in the cloud.” Precisely.
If that question cannot be answered with confidence, the company does not have sufficient visibility into its own video infrastructure.
2. Can we prove who accessed what – and when?
Not in theory. In evidence.
If internal stakeholders cannot reconstruct relevant actions around sensitive video content, then the company has convenience, but not control.
3. Would this platform survive a serious legal, security, and procurement review today?
Not a light-touch business review. A real one.
If the answer is uncertain, the risk is not that the platform will break tomorrow. The risk is that the organization has built important workflows on infrastructure it cannot fully defend.
Those are not marketing questions.
They are governance questions.
Video hosting is an infrastructure decision
That is the central reframing.
Video hosting in regulated industries is not mainly a communications choice. It is an infrastructure choice with compliance consequences. Not because video itself is exotic, but because it increasingly carries training logic, policy communication, operational knowledge, and sensitive business context.
Generic platforms do not fail because they are poor products. They fail because they were built for a different category of use.
That is an important distinction.
The good news is that the market has changed. Companies no longer have to choose only between broad public platforms and cumbersome legacy systems. There are now enterprise-oriented alternatives built around stronger governance, clearer hosting models, EU-based infrastructure options, controlled access, and multilingual workflows that fit real corporate use cases more naturally.
That is where platforms such as alugha become relevant – not as a flashy replacement for public distribution, but as a better fit for organizations that need secure internal communication, stronger data sovereignty, and enterprise video workflows that can withstand scrutiny.
Shortly put: who treats video as infrastructure should choose infrastructure accordingly.
Back to the Main Article: The Complete Guide to Enterprise Video Hosting